So I jumped into the middle of FB Oauth there, so thought I would back up a little.
Oauth is big and scary, but also quite simple as Bubble users tend to access it in the same way because most Bubble apps are web pages. So once you get it … you get it.
The difficulty with thinking about how it works, from a Bubble perspective, is that you have to split your app in two for the purposes of understanding the “dance”.
If you are a traditional developer, with a split between the front and back end devs (you may not even be in the same country, let alone the same room), it is much easier to think about.
So…Your app has two parts, the web page bits and the workflow bits.
Now for the tricky bit… we don’t trust the web page bits. Bad guys can mess with it. We DO trust the workflow bits. Which is odd for us as they are all the same app as far as we are concerned.
Ok, so this is problem, as the trusted bit isn’t in the browser. And we need the browser to be able to redirect the user to another browser page (to log in) and then back to our page.
So we give the browser some of our information, and let it ask Facebook to sign our user in. It does that by simply asking to go a facebook webpage (ok, it isn’t exactly a “page”, but it looks like one for our purposes).
If you are fast enough, you can grab the redirect URL when you hit the “sign up with Facebook” button. And actually you could dispense with Bubble entirely and just take your user to that URL.
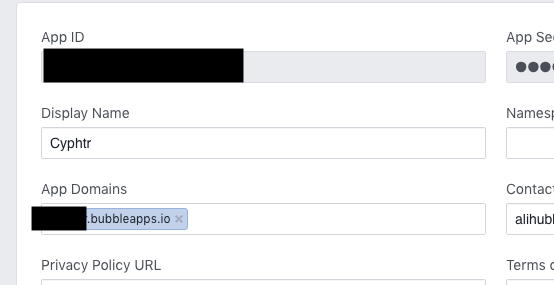
Off we go to the “authorise page”. We tell it who we are (client id, this is totally not secret) and what we want to do (scopes) and where to come back to (redirect_uri).
Our untrusted web page hasn’t got anything secret to worry about. It is easy to replace your webpage with my webpage. I can use your client id as much as I like. This is all public.
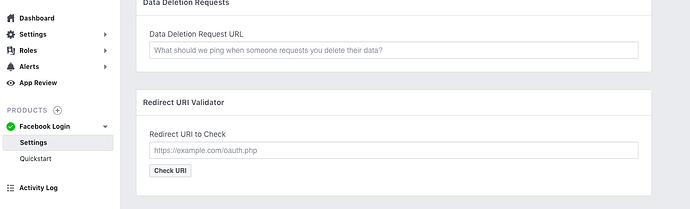
Facebook’s authorisation page checks out the client_id (yeah, looks legit) and then matches the URL you said to come back to against the list it has. It has to match exactly, and will get fussy about version-test and ?debug_mode and whether it is http or https.
So if you are having redirect url issues - try to grab the browser URL just after you hit the signup button. That will have the redirect URL in there. Now carefully check that against your app settings in the dev console.
Right, so we check out OK. Facebook asks the user to login, and then it passes control back to the page you specified. And it also passes back a code. Not a secret, it is still in our browser address so I can easily steal as many of your codes as I like. But unique.
We now have to do the secret bits, not trusted to the browser. Our web page passes this code to the back end.
The back end now has a “machine to machine” chat with facebook’s “token” service.
“Hey Facebook, my untrusted front end reckons it asked you for a code, and you gave it this Oh by the way here are my secret passcodes to ensure you know I am who I say I am. Just between you and I, is this legit ?”.
“Yes, that all checks out. Here is really secret token but please keep it really safe and don’t tell your front end”.
And then…
“Hey Facebook’s User details service, I have this super secret token, can you tell me everything about this user please”.
“Sure, that still checks out, here you go”.
In fact Bubble doesn’t even really trust us all that much, so we never get to see that super secret token in most normal situations. It hides it from us.